This research report demonstrates how domain name abandonment poses a significant cyber threat to the legal profession and other businesses. This report also makes recommendations as to measures legal practices and other businesses can take to stop this threat.
Tag: breach

Is Your Conveyancing Practice Secure From Hacking?
The recent media reports of fraud against conveyancing practices suggest that professionals should be taking measures for protecting their businesses from cyber attacks. Cybercriminals primarily rely on an email-based attack know as phishing to help commit payment redirection fraud.

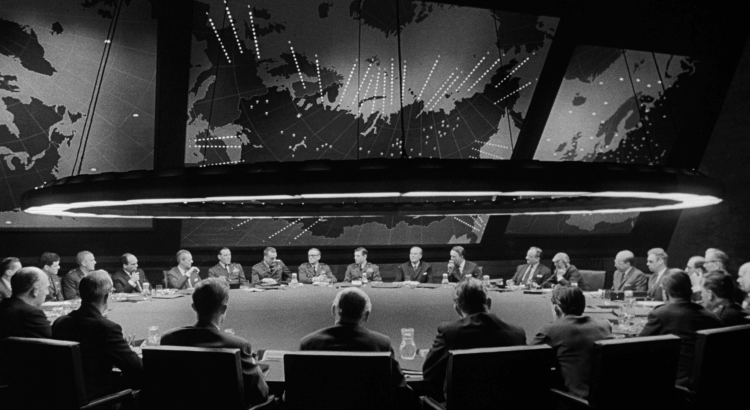
Command-and-Control Malware Traffic Playbook
Malicious actors operate command-and-control (C&C/C2) servers to interact with their victims’ computers. These C2 servers are intended to instruct the compromised PCs to do undesired things, such as stealing the user’s passwords, encrypting the files for ransom or attacking other computers on the network.

Should SOCs monitor application or infrastructure logs for suspicious events?
We learned from the previous article that SOCs/Incident Response teams should be looking for threats that represent high-level risks to the normal business activities.
We know the who, but how can we define what needs to be protected?
Assume your company has over a thousand business applications. They are hosted in multiple data centres as well as in the cloud. There are Windows and Linux hosts, and many of these are not patched of course. On top of that, nobody knows who owns them.
The following article cuts through this complexity and explains a simple approach.
Risk-Driven Incident Response
Psst! Do you wanna protect your company from security incidents?
But what you have is hundreds of apps, your infrastructure looks like a bowl of spaghetti and the company is short on resources? Don’t worry, it’s doable with careful planning!
This risk-based incident response framework lets you target the most critical things at your organisation. Keep on reading and your incident response team will operate as a powerful sniper rifle, rather than a clunky shotgun.
Checklist for Incident Response Teams
Forming a Computer Security Incident Response Team (CSIRT) is a complex affair. It normally involves a certain combination of staff, processes and technologies.
However the essentials are the same in most situations, no matter what the mission of your CSIRT is. This publication attempts to provide a list of must-have technologies for all forming incident response teams out there.
