Enforcing Two-factor Authentication (2FA) on your email service is a robust security measure that can prevent payment redirection fraud. In the following article, we demonstrate how you can enable this powerful security feature on your corporate email accounts.
Tag: two-factor

How to Protect Your Legal Practice from Payment Redirection Fraud
Learn why Australian legal professionals are high-value targets for cybercriminals and why you should be concerned. You will learn how and why money transfer scams work, and practical steps you can take to avoid becoming a victim of fraud.
Cybersecurity Tips for Conveyancers and Solicitors using PEXA
A former MasterChef finalist and her family had $250,000 stolen from a property purchase transaction on the PEXA platform at settlement recently. We explain the most likely way the fraud occurred and what practical things you can do today to protect your business from similar attacks.
Bypassing WordPress Login Pages with WPBiff
Two-factor authentication protected WordPress login pages can be bypassed because of certain unsafe NTP practices.
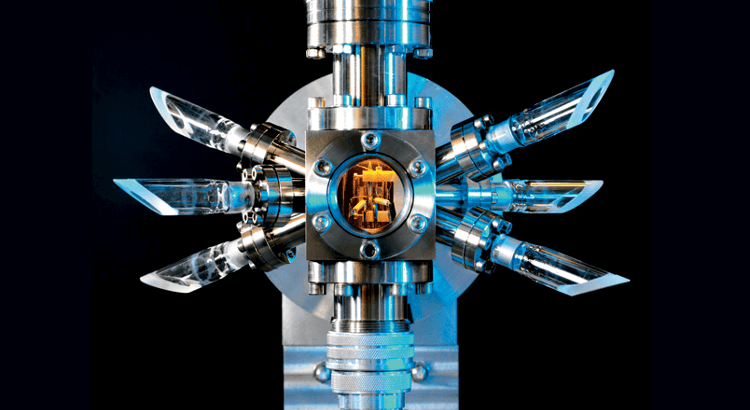
The Internal clock of remote servers can be manipulated under the right conditions. Because certain WordPress Google Authenticator plugins also rely on the local timestamp, it opens up new ways to circumvent the user authentication process on the /wp-admin dashboard.
We demonstrate a practical attack against two-factor protected WordPress login pages. We are going to gain access to the dashboard without having access to the token generator app.
Tricking Google Authenticator TOTP with NTP
Because of unsafe NTP practices, internal clocks on remote machines can be manipulated under the right conditions. Once time is altered, expired SSL certificates become valid again and causes HSTS policies to expire.
But what about authentication? Certain TOTP implementations such as popular WordPress plugins also rely on the local timestamp.
This article demonstrates a proof of concept for accessing two-factor authentication protected WordPress dashboards.

Suit Up and Protect WordPress
In the final part of the series, I am going to show a few practical tips and tricks for protecting your WordPress blog. We have seen earlier how a simple XSS vulnerability can lead to the total compromise of the hosting environment. We not only managed to deploy a backdoor, dump all data from the databases and retrieve each file from […]
