What cyber threats the future brings to us? An analysis of the cybersecurity strategies of Canada, New Zealand, the UK, the US, and Australia.
Tag: governance

Grand List of Incident Management Frameworks
Forming a Computer Security Incident Response Team (CSIRT) is a complicated affair. It involves a certain combination of staff, processes and technologies.
Luckily, numerous incident management frameworks are available for the rescue. They all aim to provide a structured approach for establishing incident response teams in your organisation.
This post provides a general overview of the most popular incident management frameworks.
Risk-Driven Incident Response
Psst! Do you wanna protect your company from security incidents?
But what you have is hundreds of apps, your infrastructure looks like a bowl of spaghetti and the company is short on resources? Don’t worry, it’s doable with careful planning!
This risk-based incident response framework lets you target the most critical things at your organisation. Keep on reading and your incident response team will operate as a powerful sniper rifle, rather than a clunky shotgun.

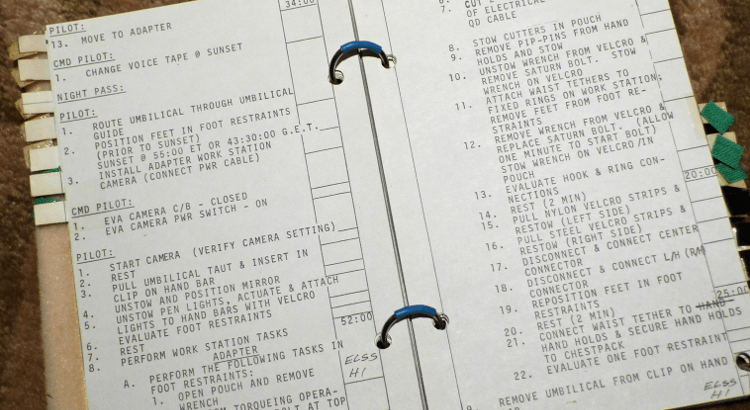
Writing Incident Response Runbooks
Incident response runbook (aka. playbook, “use case”) is a written guidance for identifying, containing, eradicating and recovering from cyber security incidents.
Check out this practical guide that walks you through the runbook development process for tackling phishing campaigns.
5 Tips on Writing Security Policies
Even pure technologists have to write security policies in an enterprise environment. As a subject matter on something, technology experts might be asked to contribute to the Software Development or the Internet Acceptable Use policies.
However this leads to policies that nobody reads. Copy-and-paste texts, dry language and 60-page long documents. Rings a bell, anyone?
In the following post I reveal a few tricks up my sleeves for writing simple, crystal-clear and straightforward security policies.
